Maria Pallante
3 Considerations for Fraud Prevention & Detection in Loyalty Programs

Over the last few months, fraud prevention and detection have been coming up to a greater extent with clients. As consumers become savvier, this becomes an ever-increasing challenge. So, if you’re launching a loyalty program, here are two questions you’ll need to think about:
What measures can be put in place to prevent fraudulent activity?
And knowing that you’ll never be able to think of everything, what can be put in place to detect or alert you to fraudulent activity?

1. Prevention: Business Rules That Limit Gaming
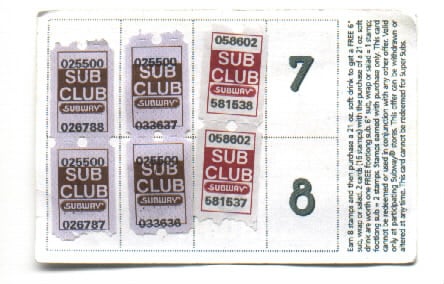
The best way to prevent fraud is by considering the opportunities for fraud in the program construct and using business rules to limit those opportunities. For instance, in a traditional loyalty program construct, there are both earning and redemption mechanics, so you should always include business rules for these. An example of a traditional loyalty program suffering from fraud was Subway’s Sub Card — which was a stamp-and-booklet type of redemption. Unfortunately, the stamps were able to be counterfeited, and there were also issues with internal staff stealing stamps and selling them. Subway didn’t realize that its program was under attack, until it discovered there were more free sandwiches being given out than were being purchased.
Here are some specific examples of business rules for earning and redemption:
Earning Mechanics: Include limits based on unusual frequency. For example, a program that awards points for visits should ensure there is a limit to the number of earning opportunities in a given timeframe or implement a minimal dollar threshold associated with each visit to ensure it is legitimate (e.g. earn when you spend $25 or more per visit with a maximum of 2 earning visits per week).
Reward/Redemption Mechanics: If your systems aren’t integrated in real time, you need to think about what that means in terms of your vulnerability. Consider what’s on offer and make sure your program/company is protected. For instance, you can limit exposure just by having the program reward direct spend-back in-store or online, and have a minimum spend requirement and expiration on the coupon (e.g. $5 off coupon toward a $50 purchase at your retail location, expiring in 10 days).

2. Employee and Vendor Operators
While we often think of fraud being committed by members, we have to always think about how employees or vendor operators may use their knowledge or access to benefit inappropriately. This is a consideration beyond loyalty programs. A recent example of costly internal fraud happened to luxury retailer Saks Fifth Avenue, where five members of an identity theft ring of sales clerks purchased over $40,000 of designer shoes, handbags and accessories with stolen credit card information from over 20 Saks customers.
Suggested business requirements for your loyalty program platform:
Automatic logging – Any time a member’s profile is accessed through administrative tools, the employee/vendor operator should be logged along with any associated activity.
Permissions/Thresholds – If point adjustments are allowed, establish thresholds based on an employee’s/vendor’s role.
Reporting – Make online reports available to track adjustments, earning and redemption by employees and vendors.
3. Detection: Alerts and Reporting
Since full prevention is impossible within a program, detection of inappropriate activity is important. Establishing email alerts to a defined group of individuals when unusual activity occurs is a best practice. This will allow the team to address detected issues in a timely manner. Regular monitoring of trends and reports also support detection of issues. For example, if alternate shipping addresses are allowed in a program where merchandise is shipped, an alternate shipping report will provide an opportunity for a visual check that nothing unusual is happening, such as an employee redeeming from a member’s account and shipping to a personal address.
Final Thoughts
While a lot of the thinking related to fraud occurs during the launch of a program, as a program evolves or new scenarios present themselves it is important to continue to revisit these measures and ensure they are updated. These present opportunities to refine processes and business rules, and adjust detection and reporting protocols.